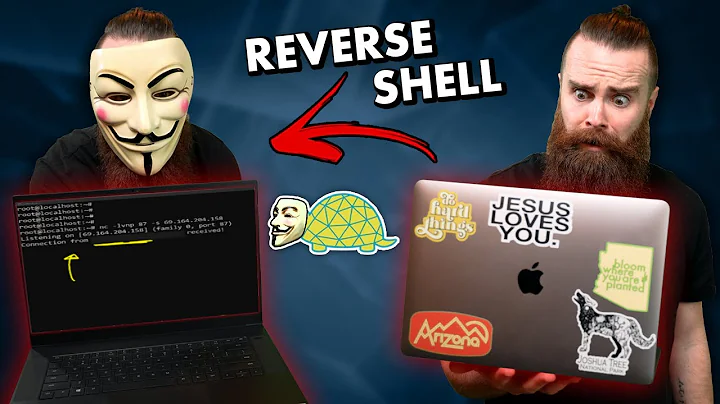
How Do Bind Shells Work? - How To Create A Bind Shell (backdoor Example) #cybersecurity
Synopsis
Want to learn how hackers use shells and payloads in cybersecurity? In this tutorial, we break down the differences between bind ...
Download Options
Choose a download method below. All links open in new tabs.
| Service | Features | Action |
|---|---|---|
| Ssvid |
MP4 & MP3 • HD Quality • Browser Extension Available
|
Download |
| SaveFrom |
MP4 & MP3 • HD Quality • Browser Extension Available
|
Download |
Security Notice: These are third-party services. We recommend using antivirus software and being cautious of pop-up ads.